Microcorruption CTF Hanoi Write-up
- 2 minsSummary:
This is a write-up of my solution to the Microcorruption CTF challenge “Hanoi” (LOCKIT PRO r b.01).
Let’s jump right in…
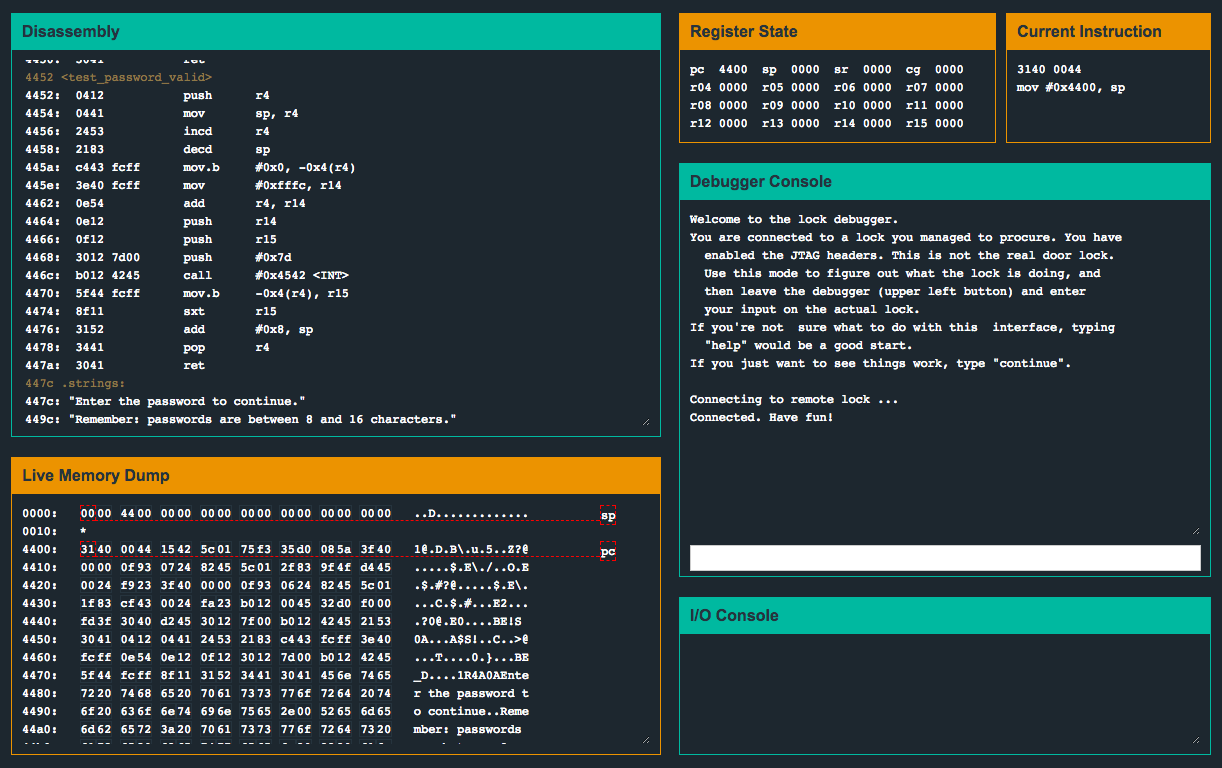
4438 <main>
4438: b012 2045 call #0x4520 <login>
443c: 0f43 clr r15main() this time only makes a call to a function called login(). Let’s dissect login():
Straight away, the instruction at 0x455a catches my eye, cmp.b #0xc7, &0x2410. Ultimately, this instruction will compare the byte located at memory address 0x2410, with the value 0xc7, and if they are equal, the door will unlock. Let’s set a breakpoint on the instruction and inspect the memory region around 0x2410 when execution pauses.
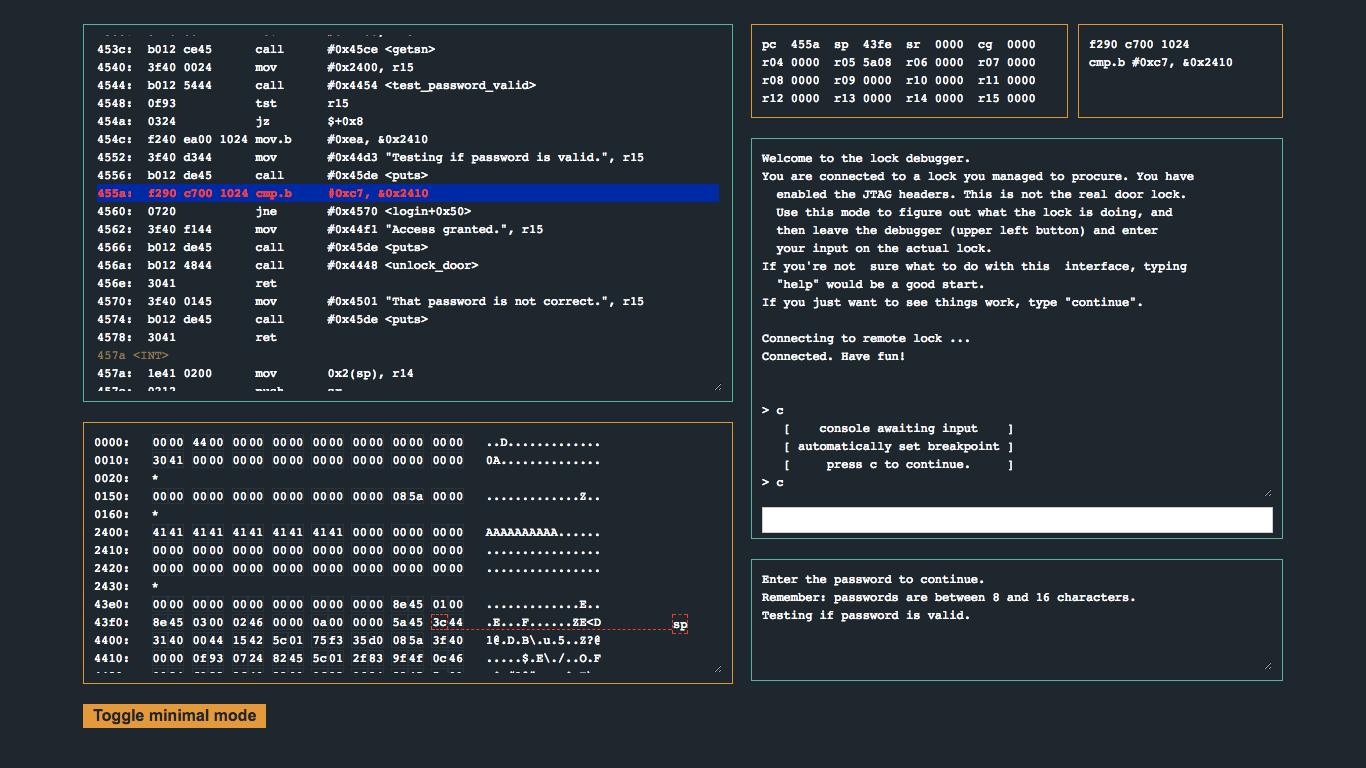
When being prompted for the password, I used AAAAAAAAAA. Check out the memory dump and notice where our input is (hint 0x2400). Notice that right after the 16th byte, the 17th byte will land in 0x2410. Great! Although the password prompt says to use a password of length 8 to 16 characters, let’s try using a 17-byte password and attempt a one-byte overflow into 0x2410 with 0xc7 and see if we can unlock the door…
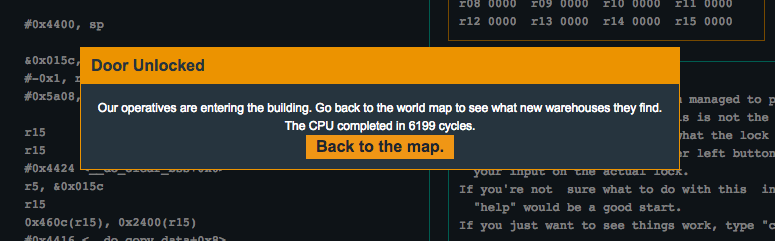
Flag (mouse over to reveal)
41414141414141414141414141414141c7
