Microcorruption CTF New Orleans Write-up
- 3 minsSummary:
This is a write-up of my solution to the Microcorruption CTF challenge “New Orleans” (LOCKIT PRO r a.01).
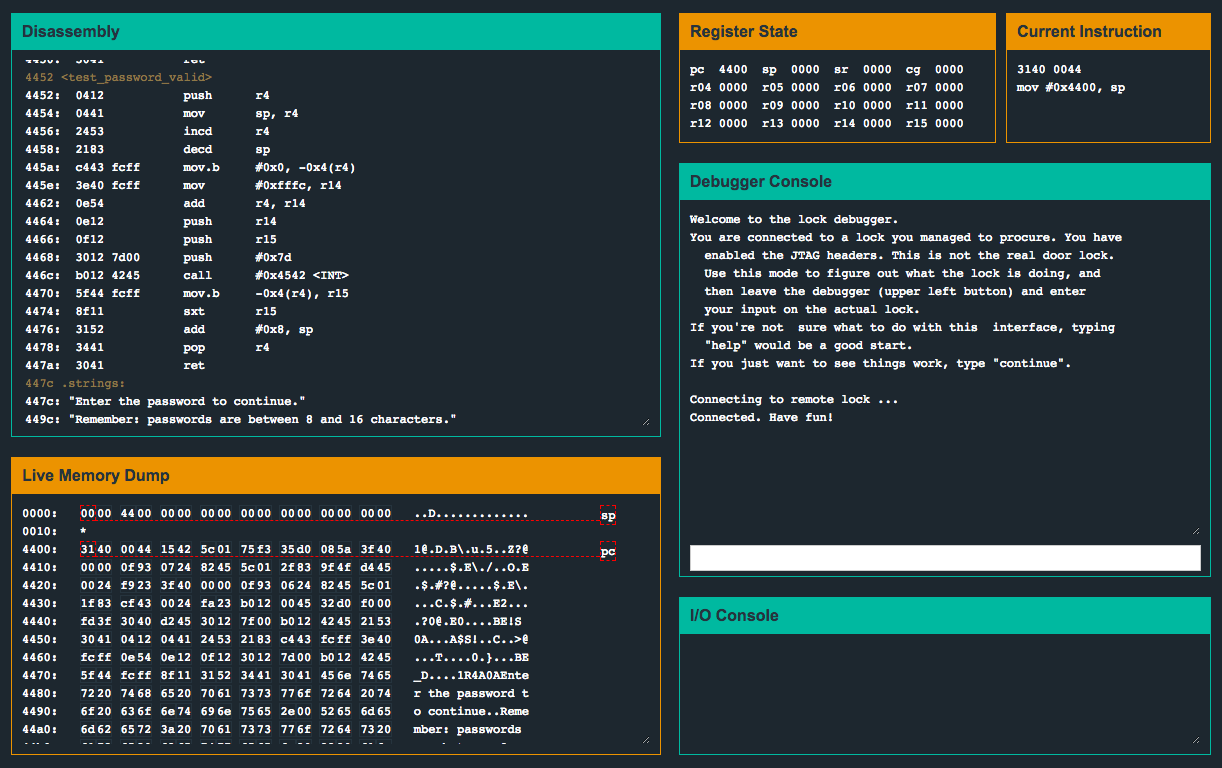
Let’s begin by first taking a look inside the main function:
A few things look interesting. First, a call to a function called create_password(), then eventually a call to a function called check_password(). We can see that after the call to check_password(), r15 is compared with zero. If r15 is not zero, execution will jump to 0x4462, which will print the access granted message and will call the unlock_door() routine. First, let’s see what create_password() is doing:
We can see that 8 bytes are being loaded into the memory location at 0x2400. Cool. Let’s keep this in mind and check out what’s going on inside check_password():
We can see that the instruction cmp.b @r13, 0x2400(r14) will compare the memory location pointed to from r13 (the location of the first byte of our input) with the byte located at memory address 0x2400 (the location of the memory containing 8 bytes set by the previous call to create_password()). These instructions will then loop, comparing each byte from memory with a byte from the input. If the comparison does not succeed, the following instruction jne #0x44d2 <check_password+0x16> will jump the execution to 0x44d2, which will clear the r15 register and return to main(). Because r15 contains 0 at this point, the subsequent tst instruction (in main()) will fail and execution will not reach unlock_door(). However, if the byte comparisons succeed, 0x1 will be loaded into r15, and execution will return to main() at which point the tst instruction will succeed. Let’s input the bytes that we noted from the call to create_password() and see what happens…
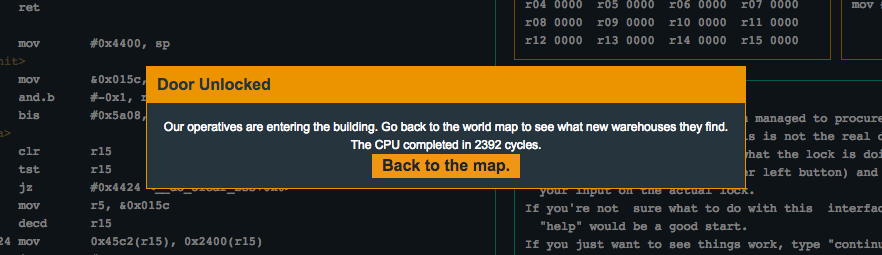
Flag (mouse over to reveal)
B<[FZ@A
